- Community Home
- >
- Networking
- >
- Switching and Routing
- >
- Aruba & ProVision-based
- >
- Re: Configure HP Aruba 2530G acl to permit NTP
Categories
Company
Local Language
Forums
Discussions
Forums
- Data Protection and Retention
- Entry Storage Systems
- Legacy
- Midrange and Enterprise Storage
- Storage Networking
- HPE Nimble Storage
Discussions
Discussions
Discussions
Forums
Discussions
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
- BladeSystem Infrastructure and Application Solutions
- Appliance Servers
- Alpha Servers
- BackOffice Products
- Internet Products
- HPE 9000 and HPE e3000 Servers
- Networking
- Netservers
- Secure OS Software for Linux
- Server Management (Insight Manager 7)
- Windows Server 2003
- Operating System - Tru64 Unix
- ProLiant Deployment and Provisioning
- Linux-Based Community / Regional
- Microsoft System Center Integration
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Community
Resources
Forums
Blogs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 06:37 AM - last edited on 10-22-2021 08:25 PM by support_s
10-22-2021 06:37 AM - last edited on 10-22-2021 08:25 PM by support_s
Configure HP Aruba 2530G acl to permit NTP
Hello people!
I am running HP Aruba 2530G with 16.10 firmware and am stuck at configuring ACLs to permit udp/123 for time synchronisation.
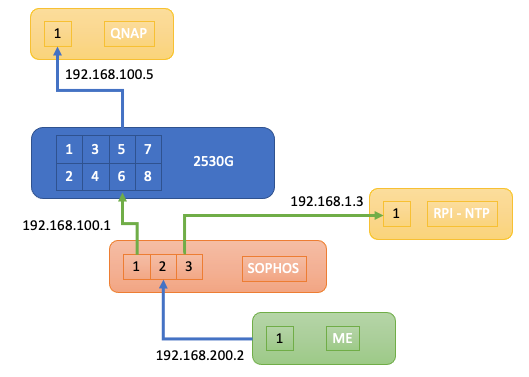
My network:
Sophos Firewall is handling routing between VLANs via InterVLAN routing. The 2530G connects to one of the ports on the FW.
The NTP server is located on another VLAN connected to the FW: NTP Server IP Addr 192.168.1.3
- The configuration for the 2530G is as follows.
- Interface 6 connects to the FW (IP Addr: 192.168.100.1 also gateway for the subnet)
- Interface 5 connects to a QNAPNAS. (192.168.100.5)
- Interface 4 connects to another HP Aruba Switch (192.168.100.3)
- Interface 3 - I am on this interface with IP Addr 192.168.100.2)
The 2530G also has 192.168.100.1 configured as the gateway.
I have the following ACL on Interface 6
ip access-list extended "Permit SNTP NTP udp/123 from QNAP to NTP"
10 permit udp 192.168.100.5 0.0.0.0 192.168.1.3 0.0.0.0 eq 123 log
20 permit tcp 192.168.100.5 0.0.0.0 192.168.1.3 0.0.0.0 eq 123 log
exit
Without the ACL, the QNAP NAS was able to connect to the NTP server at 192.168.1.3.
But with the above ACL, SNTP/NTP does not connect.
Am I missing something?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 06:57 AM
10-22-2021 06:57 AM
Re: Configure HP Aruba 2530G acl to permit NTP
Hmm... the ACL on interface 6 was
ip access-group "Permit SNTP NTP...." in
Does this mean the ACL applies only to packets coming into Interface 6? How should i allow outgoing packets on Interface 6?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 07:15 AM
10-22-2021 07:15 AM
Re: Configure HP Aruba 2530G acl to permit NTP
I think this may need to be applied to Interface 5 instead of Interface 6, as the ACL is applied on the inbound.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 07:55 AM
10-22-2021 07:55 AM
Re: Configure HP Aruba 2530G acl to permit NTP
Exactly! On port 6 the incoming traffic is coming from the firewall and there will be no matches with the source IP of the QNAPNAS. This ACL is blocking everything from the firewall. If you dont see the option "out" after access-group, it means that 2530 doesnt support port ACL in outbound direction.
Then in this case you should apply the ACL to the port where you connect the end device that should be controlled -QNAPNAS. BUt keep in mind that this ACL only allows NTP traffic and blocks all other traffic. If this is all that is needed for the QNAPNAS then it is OK but if other types of traffic should be allowed you should add more rules.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 08:38 AM
10-22-2021 08:38 AM
Re: Configure HP Aruba 2530G acl to permit NTP
Cool - I'll test this out tmrw and get back
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 09:26 AM
10-22-2021 09:26 AM
Re: Configure HP Aruba 2530G acl to permit NTP
I'm pretty sure the 2530G does not support outgoing ACLs in the interface. Wouldn't the last implicit rule block all ip addreesses going out too?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 11:28 AM
10-22-2021 11:28 AM
Re: Configure HP Aruba 2530G acl to permit NTP
Hello,
Yes, I also checked. An ACL on 2530 can be applied only inbound on ports and VLANs. That means it is applied on packets entering the switch via the specified interface. Not on packets which are scheduled to leave the switch out of this ports. The implicit deny rule at the end also controlls only inbound traffic. Outbond traffic is not affected.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 08:29 PM
10-22-2021 08:29 PM
Re: Configure HP Aruba 2530G acl to permit NTP
Hello Emil_G,
I've tested the 2530G acls in multiple configuration and regretfully report that the ACL implicit deny also blocks outgoing packets.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 11:34 PM
10-22-2021 11:34 PM
Re: Configure HP Aruba 2530G acl to permit NTP
Hello,
This shouldnt be the case and it is strange if it happens. Maybe you can share some details on how exactly you determined this?
We have to keep in mind that most communication protocols especially TCP based are 2 way communication. In order for a session to be established you typically need some sort of a handshake (for example the TCP 3 way handshake) and ongoing acknowledgement between the communicating computers. If one direction is blocked by the ACL this handshake cannot be performed and the session cannot establish no matter from which peer (that means in which direction) the session is started. The result would be that the protocol is blocked and this may lead to wrong conclusions about how the ACL is functioning. This could be a possible explenation.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2021 08:26 PM
10-23-2021 08:26 PM
Re: Configure HP Aruba 2530G acl to permit NTP
Hello Emil_G
Interface 6 - connects to the FW (IP Addr: 192.168.100.1 also gateway for the subnet)
Interface 5 - connects to a QNAPNAS. (192.168.100.5)
Interface 4 - connects to another HP Aruba Switch (192.168.100.3)
NTP Server is sitting on 192.168.1.3 (accessible via 2530G interface 6 only)
I'm sitting on 192.168.200.2 (accessible via 2530G interface 6 only)
Tested using the following scenario on interface 6, with no other ACLS on any other interfaces
ip access-list extended "Permit QNAP MGT Page from QNAP to NTP"
10 permit tcp 192.168.200.2 0.0.0.0 192.168.100.5 0.0.0.0 eq 443
20 permit tcp 192.168.200.2 0.0.0.0 192.168.100.5 0.0.0.0 eq 80
exit
The above ACL could only be applied inbound to interface 6
I (sitting on 192.168.200.2) was able to connect to the ports 80, 443 on 192.168.100.5
But I could not update the NTP server time on 192.168.1.5 with the above ACL applied to interface 6.
What about Interface 5?
I didn't apply any ACLs on Interface 5 so this should allow all port access.
That's how I came to a conclusion (whether rightfully or wrongfully), the 2530G's ACL implicit deny rule blocks all traffic whether in or out.