- Community Home
- >
- Storage
- >
- Midrange and Enterprise Storage
- >
- HPE 3PAR StoreServ Storage
- >
- LDAP Authentication Issues
Categories
Company
Local Language
Forums
Discussions
- Integrity Servers
- Server Clustering
- HPE NonStop Compute
- HPE Apollo Systems
- High Performance Computing
Knowledge Base
Forums
- Data Protection and Retention
- Entry Storage Systems
- Legacy
- Midrange and Enterprise Storage
- Storage Networking
- HPE Nimble Storage
Discussions
Knowledge Base
Forums
Discussions
- Cloud Mentoring and Education
- Software - General
- HPE OneView
- HPE Ezmeral Software platform
- HPE OpsRamp Software
Knowledge Base
Discussions
Forums
Discussions
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Community
Resources
Forums
Blogs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-13-2014 07:52 AM - edited 11-13-2014 07:56 AM
11-13-2014 07:52 AM - edited 11-13-2014 07:56 AM
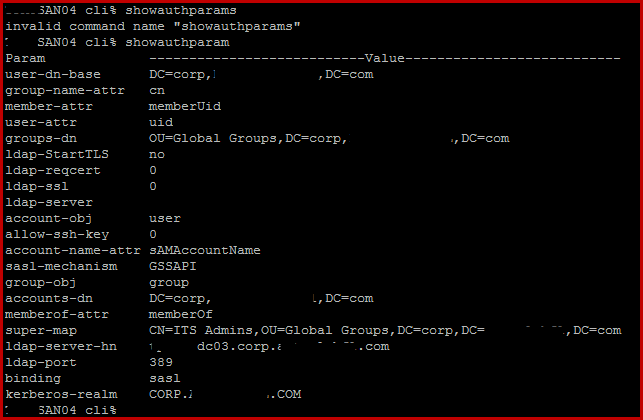
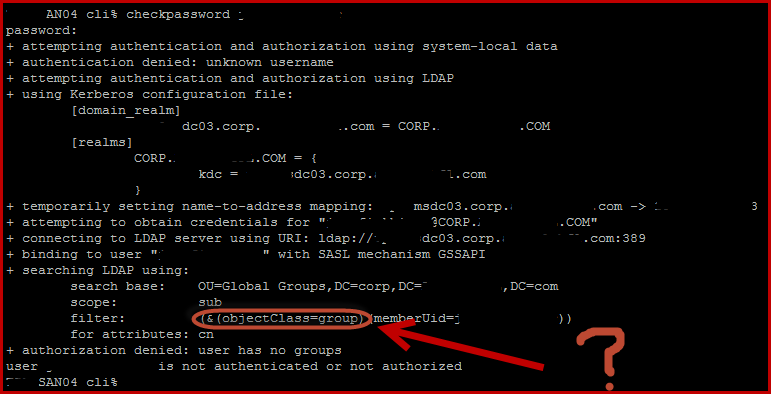
I am having some issues with setting up authentication. I am doing the checkpassword command with one of my domain accounts and the "searching LDAP using:" looks questionable. The filter seems to be attempting to filter on objectClass group not user and I am not sure why. I am currently trying to authenticate to an Windows 2012 R2 Active Directory Server. I have included some screen shots with vital info redacted.
showauthparam:
checkpassword:
Solved! Go to Solution.
- Tags:
- LDAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-17-2014 11:55 AM
11-17-2014 11:55 AM
SolutionSo I ended up having to punt on this one. I went through the CLI reference guide for 3.2.1 MU1 and I found the command to clear all auth params. I ran the following command:
setauthparams -f -clearall
Once I did that I ran through the setauthparams again. I used the following commands, in the following order:
setauthparam -f ldap-server <ipaddress of domain controller to use>
setauthparam -f ldap-server-hn <DNS_Hostname of DC, case insensitive>
setauthparam -f kerberos-realm <LDAP_Service name, case sensitive. Use LDP.exe on DC and pull value from the output connecting to the DC>
setauthparam -f binding sasl
setauthparam -f sasl-mechanism GSSAPI
setauthparam -f accounts-dn <dn path, you can pull DN path from adsi or the attributes tab in ADUC if you have advanced mode enabled>
setauthparam -f account-obj user (This value needs to be "user" specifically for AD)
setauthparam -f account-name-attr sAMAccountName (if you look at page 22 on the CLI Admins Reference guide for 3.2.1 MU1 this value says "sAMAccount". This is completely wrong. Windows AD requires sAMAccountName)
setauthparam -f memberof-attr memberOf
setauthparam -f <map_param> <map_value, DN of group that you wish to reference in AD>
In some writeups the following is listed as a required command
setauthparams -f account-group group
Do not use that command. It triggers the filter for parsing Active Directory to change to "group" instead of authenticating per user. That's essentially what was throwing off my AD configuration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-23-2014 09:32 PM
11-23-2014 09:32 PM
Re: LDAP Authentication Issues
Hi,
Very well Self Solved..:)
Here is the script to set up LDAP:
Just replace the info with the customers info REM assuming all windows default security params REM setauthparam ldap-server <IP-Address> REM setauthparam ldap-server-hn <DNS-hostname> REM setauthparam kerberos-realm <LDAP-ServiceName> - CASE SENSITIVE REM setauthparam binding sasl REM setauthparam sasl-mechanism GSSAPI REM setauthparam accounts-dn <dn-path> REM setauthparam account-obj user (tells the LDAP client to search for users) REM setauthparam account-name-attr SAMAccountName REM setauthparam memberof-attr memberOf REM checkpassword ---- REM EXAMPLE USING THE LAB MACHINES ---- REM assuming all default windows params REM clear out all old params setauthparam -f clearall setauthparam -f ldap-server 192.168.47.100 setauthparam -f ldap-server-hn mktg-admin0.3par-mktg.3pardata.com setauthparam -f kerberos-realm 3PAR-MKTG.3PARDATA.COM setauthparam -f binding sasl setauthparam -f sasl-mechanism GSSAPI setauthparam -f accounts-dn cn=Users,dc=3par-mktg,dc=3pardata,dc=com setauthparam -f account-obj user setauthparam -f account-name-attr sAMAccountName setauthparam -f memberof-attr memberOf setauthparam super-map "cn=Domain Admins,cn=Users,dc=3par-mktg,dc=3pardata,dc=com"
Regards,
PS
PS
To assign points on this post? Click the white Thumbs up below!