- Community Home
- >
- Servers and Operating Systems
- >
- HPE ProLiant
- >
- ProLiant Servers (ML,DL,SL)
- >
- ILO LDAP Configuration not working
Categories
Company
Local Language
Forums
Discussions
Forums
- Data Protection and Retention
- Entry Storage Systems
- Legacy
- Midrange and Enterprise Storage
- Storage Networking
- HPE Nimble Storage
Discussions
Forums
Discussions
Discussions
Discussions
Forums
Discussions
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
- BladeSystem Infrastructure and Application Solutions
- Appliance Servers
- Alpha Servers
- BackOffice Products
- Internet Products
- HPE 9000 and HPE e3000 Servers
- Networking
- Netservers
- Secure OS Software for Linux
- Server Management (Insight Manager 7)
- Windows Server 2003
- Operating System - Tru64 Unix
- ProLiant Deployment and Provisioning
- Linux-Based Community / Regional
- Microsoft System Center Integration
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Community
Resources
Forums
Blogs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 08:31 AM - edited 04-14-2020 08:33 AM
04-14-2020 08:31 AM - edited 04-14-2020 08:33 AM
Hi there,
i´m trying various different ways on connecting our ILOs to Active directory using LDAP.
So far everytime i configure a new ILO it works for a couple of minutes but then breaks. After that i´m unable to make it working again. I tried with ILO3 - ILO5 in various different firmware levels but for whatever reason it keeps breaking.
from the ILO5 test im getting the line
Connect to Directory Server Success
Connect using SSL Failed Error code 0 (ok). Consult the Integrated Lights-Out User Guide for details. Error code 0 (ok) seems good to me?!
So there is no real reason for me why that should stop here as error code 0 is fine ?!
Has anyone gotten this to work?
BR
Johannes
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2020 12:20 AM
04-21-2020 12:20 AM
Re: ILO LDAP Configuration not working
Hi Johannes,
Kindly verify the pre-requisities mentioned in the user guide and provide us with the outcome.
Prerequisites for configuring authentication and directory server settings:
1.Verify that your iLO user account has the Configure iLO Settings privilege.
2.Install an iLO license that supports this feature.
3.Configure your environment to support Kerberos authentication or directory integration.
4.The Kerberos keytab file is available (Kerberos authentication only).
For more information please refer HPE iLO 5 User Guide (Page number 249 - 256)
Link: https://support.hpe.com/hpesc/public/docDisplay?docId=a00018324en_us
BR,
Shruthi
I work at HPE
HPE Support Center offers support for your HPE services and products when and how you need it. Get started with HPE Support Center today.
[Any personal opinions expressed are mine, and not official statements on behalf of Hewlett Packard Enterprise]

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2020 12:43 AM
04-21-2020 12:43 AM
Re: ILO LDAP Configuration not working
Hi,
I only want to use LDAPs and no Kerberos till now and from what I understand this is not a requirement?
All the other things are correct implemtented.
From what i was seeing is that the Directory User Context is not working with our Active Directory LDAP.
Another problem seems beeing that the test is failing but login works just fine.
BR
Johannes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2020 10:49 PM
04-27-2020 10:49 PM
Re: ILO LDAP Configuration not working
Hi,
Please log a case with the HPE support team for further assistance on this since the pre-requirements are already met.
Link to log a case: https://support.hpe.com/portal/site/hpsc/scm/home?ac.admitted=1470780193089.125225703.1938120508
Br,
Shruthi
I work at HPE
HPE Support Center offers support for your HPE services and products when and how you need it. Get started with HPE Support Center today.
[Any personal opinions expressed are mine, and not official statements on behalf of Hewlett Packard Enterprise]

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 09:42 PM - edited 04-28-2020 09:45 PM
04-28-2020 09:42 PM - edited 04-28-2020 09:45 PM
Re: ILO LDAP Configuration not working
Hi Johannes
The certificates on the domain controllers must use 1024-bit encryption and not 2048-bit encryption. As per Microsoft KB article Q321051 the private keys must not have strong protection enabled to be able to use third party LDAP over SSL authentication. For authentication to work correctly between iLO and the domain controller in AD, the domain controller must have LDAP over SSL capabilities. This means the domain controller must have a certificate assigned by a Certificate Authority. See the Microsoft Knowledge Base for more information on installing a Certificate Server on a domain controller so that other domain controllers can automatically obtain certificates. The existing PKI infrastructure can be used to obtain certificates. For information about this, refer to Microsoft Knowledge Base article in the following URL.
Click on below link to access the article titled "How to enable LDAP over SSL with a third-party certification authority"
For an alternate method to check SSL, use the Microsoft ldp.exe tool. If AD authentication fails, check the event log for an LDAP error.
In addition above action also check by reset iLO from iLO web console.
[Any personal opinions expressed are mine, and not official statements on behalf of Hewlett Packard Enterprise]

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-29-2020 12:03 AM
04-29-2020 12:03 AM
Re: ILO LDAP Configuration not working
Hi,
i´m pretty sure we are meeting all this as there are tons of other tools connecting to our LDAPs servers.
I couldn´t find any advise to use only 1024 instead the MS KB mentions
KeyLength = 1024
; Can be 1024, 2048, 4096, 8192, or 16384.
Not sure if this is the right place here but actually the LDAP test is giving more questions then it solves, is there a way to better debug whats going on?
BR
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-04-2020 03:27 AM
08-04-2020 03:27 AM
Re: ILO LDAP Configuration not working
We too have the exact same issue.
ILOs are configured to use Active Directory LDAP via port 636
Same issue across firmware version 2.55 to 2.73 for ILO4 and 2.10 to 2.18 for ILO5.
When we reset the ILO, it works for couple of days and again the issue starts.
We already logged a case with HPE and no solutions so far.
- Tags:
- too had
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2020 06:43 AM - last edited on 08-06-2020 03:23 AM by Parvez_Admin
08-05-2020 06:43 AM - last edited on 08-06-2020 03:23 AM by Parvez_Admin
Re: ILO LDAP Configuration not working
Hi @Johannes_we ,
Hope you are doing Good.
We too have the same problem. Did you got the soultion for this issue ?
- Tags:
- i
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-07-2020 07:56 AM - edited 08-07-2020 08:02 AM
08-07-2020 07:56 AM - edited 08-07-2020 08:02 AM
Re: ILO LDAP Configuration not working
I Suspect the issue with Directory Server & Certificate Authority .
Verifying an LDAP connection using below steps.
1. Start the Active Directory Administration Tool (Ldp.exe).
2. On the Connection menu, click Connect.
3. Type the name of the domain controller to which you want to connect.
a. You must use a proper DNS name for the SSL test to work.
4. Type 636 as the port number and check the SSL box
5. Click OK.
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-07-2020 08:04 AM
08-07-2020 08:04 AM
Re: ILO LDAP Configuration not working
HI Eeswaran
Can you please let me know after how many days you see this issue ??
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2020 07:04 AM
08-12-2020 07:04 AM
Re: ILO LDAP Configuration not working
Can you please let us know the what is " Directory User Context 1" defined in iLO ??
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2020 07:06 AM
08-12-2020 07:06 AM
Re: ILO LDAP Configuration not working
Can you please let us know the what is " Directory User Context 1" defined in iLO
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2020 12:36 AM
08-18-2020 12:36 AM
Re: ILO LDAP Configuration not working
Everything is fine using ldp and actually every other tool works fine using LDAPs even these from HPE (3Par, Primera, Nimble, SSMC etc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2020 12:38 AM
08-18-2020 12:38 AM
Re: ILO LDAP Configuration not working
Hi @Eeswaran,
sorry i have no solution so far and stopped further deployment until i have a solution.
I hope this thread gets a little more tention to HPE because my case with them was not really helpful.
BR
Johannes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2020 05:34 AM - edited 08-24-2020 05:52 AM
08-24-2020 05:34 AM - edited 08-24-2020 05:52 AM
Re: ILO LDAP Configuration not working
Hi SandurMaverick,
Thanks for the reply.
LDAP connection has been verified and it is working fine.
Domain authentication with LDAP Server working fine in 100's of servers during the notification of issue in a server ILO and this ensures that there is no issue with LDAP Connection
All the servers ILO's are configured similarly.
"Directory User Context" 1 , 2 and 3 has been updated with common directory subcontexts.
Every other tools configured with the same LDAP is working fine
After Resetting the ILO, domain authentication works fine, but after sometime again the issue starts
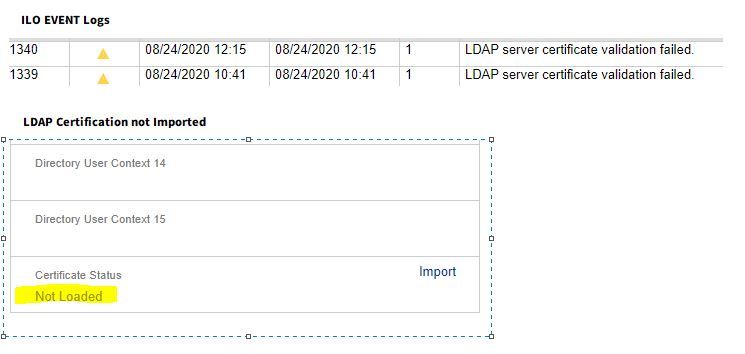
From ILO User Guide, it has been mentioned that if CA Certificate is not imported, Certificate validation step is skipped, But whereas domain login authentication fails stating that “LDAP server certificate validation failed.” Attached the screenshots for reference.
This issue exists in all generations and firmwares, 2.55 to 2.73 for ILO4 and 2.10 to 2.18 for ILO5.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 02:42 AM
08-26-2020 02:42 AM
Re: ILO LDAP Configuration not working
HI Eeswarna,
Thank you for letting us know the issue..
as per you description the issue doesn't start when configured for the first Time & Domain Login works fine.. but the issue starts when you do the iLO reset after which you are seeing an issue of domain login failure due to certificate Validation failure.. i get your point . can you confirm the domain user on which the issue is seen is actually part of How many Security Groups ..
Command : to run on Domain Controller : dsquery user -samid ilouser | dsget user -memberof | dsget group -samid
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 05:16 AM
08-26-2020 05:16 AM
Re: ILO LDAP Configuration not working
I´m having trouble with multiple users.
one is a test user only beeing in the one group + "domain users" but still having that issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-27-2020 12:26 AM
08-27-2020 12:26 AM
Re: ILO LDAP Configuration not working
Hello Johannes_we & Eeswaran,
Can you update the March 10, 2020 updates Secuirty Patches from Microsoft & See this gets resolved
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-27-2020 12:31 AM
08-27-2020 12:31 AM
Re: ILO LDAP Configuration not working
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-28-2020 07:40 AM - edited 08-28-2020 07:42 AM
08-28-2020 07:40 AM - edited 08-28-2020 07:42 AM
Re: ILO LDAP Configuration not working
HI SandurMavericK,
01. In our case we are using Service account, which is part of 2 Security groups and My Domain Account is part of many security groups. We even tested with a test account which is part of single security group. For all accounts we are receving the same issue.
02. Regarding the Microsoft March 10, 2020 patches MS has confirmed that, Updates will not make changes to LDAP signing or LDAP channel binding policies or their registry equivalent on new or existing domain controllers. Anyhow all our DC's are patched with all compatible patches released till July 2020
03. Verified the following registry in all the DC's: Security Providers is listed with 'pwdssp.dll'
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-08-2020 06:51 AM - edited 09-08-2020 06:51 AM
09-08-2020 06:51 AM - edited 09-08-2020 06:51 AM
Re: ILO LDAP Configuration not working
has there been any update? Our DC´s are all up to date.
iLO is the only LDAP "Consumer" that has trouble, all others work flawlessly including iLO Amplifier Pack, 3Par, Primera, Nimble.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2020 11:08 AM
09-13-2020 11:08 AM
Re: ILO LDAP Configuration not working
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-14-2020 01:44 AM
09-14-2020 01:44 AM
Re: ILO LDAP Configuration not working
Hello Vaitheeswaran
Can you please log a TICKET... we are not able to reproduce the issue which you are seeing ...
I work for HPE

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 04:33 AM
01-25-2021 04:33 AM
Re: ILO LDAP Configuration not working
Hi, I had the same issue with ldap auth, changing the setting "Security"->"Encryption" from "HighSecurity" to "Production" solved my issue. (Firmware 2.30/2.33)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-04-2021 12:28 AM
02-04-2021 12:28 AM
SolutionTo all out there, i think i have a solution for Active Directory LDAP Config.
Works for me for iLO 4 and iLO 5
- LDAP Schema Directory default
- Directory server address Comma seperated List of LDAP Server / Domain Controller
- Directory server port 636
- Directory user context
@domainfqdn (e.g. something.corp)
Then only the direcory group DN is needed and works like a charm.