- Community Home
- >
- Company
- >
- Advancing Life & Work
- >
- Component Authentication: The Foundation for a Sec...
Categories
Company
Local Language
Forums
Discussions
Forums
- Data Protection and Retention
- Entry Storage Systems
- Legacy
- Midrange and Enterprise Storage
- Storage Networking
- HPE Nimble Storage
Discussions
Discussions
Discussions
Forums
Discussions
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
- BladeSystem Infrastructure and Application Solutions
- Appliance Servers
- Alpha Servers
- BackOffice Products
- Internet Products
- HPE 9000 and HPE e3000 Servers
- Networking
- Netservers
- Secure OS Software for Linux
- Server Management (Insight Manager 7)
- Windows Server 2003
- Operating System - Tru64 Unix
- ProLiant Deployment and Provisioning
- Linux-Based Community / Regional
- Microsoft System Center Integration
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Community
Resources
Forums
Blogs
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Receive email notifications
- Printer Friendly Page
- Report Inappropriate Content
Component Authentication: The Foundation for a Secured Infrastructure
By Curt Hopkins, Managing Editor, Hewlett Packard Labs
In January, the U.S. Cybersecurity and Infrastructure Security Agency issued an emergency directive to mitigate DNS infrastructure tampering. This directive was necessary because the majority of security’s low-hanging fruit has already been picked. Now a smarter, better funded group of bad actors – often with nation-state or organized crime backing – is attacking the our global digital ecosystem. They are employing increasingly sophisticated techniques, requiring more advanced defense technology.
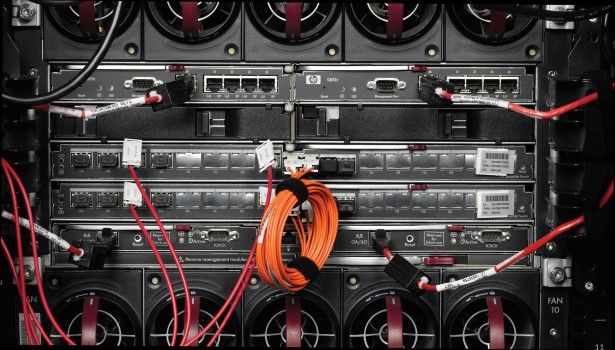
Hewlett Packard Labs Distinguished Technologist Nigel Edwards and Senior Research Engineer Theo Koulouris have written a white paper, co-authored with Michael Krause, HPE Fellow and VP, titled Component Authentication—Foundation for a Secured Infrastructure. It describes a new architecture developed by Hewlett Packard Enterprise for a secured component infrastructure that promises to harden that increasingly-targeted hardware.
This system provides strong component authentication and firmware measurement capabilities in every component and at every level, from manufacturing to integration to initialization and power cycle events to runtime and component addition or replacement.
“Our goal is to be able to authenticate everything that is in a chassis, to verify each are genuine, and in a ‘known good state,’” says Edwards. This assures customers can start off with a computing platform that is in the state it should be. After all, we are now in a time when attack vectors include device components, which contain microcontrollers and computers in their own right and run software stacks with operating systems like Linux. They designed the system to eliminate the ability of bad actors to replace good components with ones designed to conduct espionage or to otherwise damage the system, whether that systems is destined for the data center or the field.
One of the most damaging elements of malware is persistence. The harvesting of private information or the injection of harmful programming is most effective for hackers when it is done over time and without detection. With Component Authentication, that is now much more difficult.
One of the benefits of this system, says Koulouris, is that it does not require changes to existing hardware architecture. “A number of interconnects already exist within a chassis,” he says. This system is designed so that it operates over the busses and interconnects a device already uses.
“Although our primary goal is building more resilient and secure infrastructure, the system also addresses the issue of counterfeiting,” says Koulouris. Swapping out high-quality parts for inferior components – which benefits no one but the counterfeiters – will no longer be possible on a device running Component Authentication.
This is not an innovation that Hewlett Packard Enterprise is keeping locked away. HPE is sharing Component Authentication with industry consortia such as the Distributed Management Task Force and Gen-Z in the hope that it will insulate the entire industry against hardware hackers.
- Back to Blog
- Newer Article
- Older Article
- MandyLott on: HPE Learning Partners share how to make the most o...
- thepersonalhelp on: Bridging the Gap Between Academia and Industry
- Karyl Miller on: How certifications are pushing women in tech ahead...
- Drew Lietzow on: IDPD 2021 - HPE Celebrates International Day of Pe...
- JillSweeneyTech on: HPE Tech Talk Podcast - New GreenLake Lighthouse: ...
- Fahima on: HPE Discover 2021: The Hybrid Cloud sessions you d...
- Punit Chandra D on: HPE Codewars, India is back and it is virtual
- JillSweeneyTech on: An experiment in Leadership – Planning to restart ...
- JillSweeneyTech on: HPE Tech Talk Podcast - Growing Up in Tech, Ep.13
- Kannan Annaswamy on: HPE Accelerating Impact positively benefits 360 mi...