- Community Home
- >
- Storage
- >
- Around the Storage Block
- >
- HCI optimized for edge, part 6: Cost-effective dat...
Categories
Company
Local Language
Forums
Discussions
Knowledge Base
Forums
- Data Protection and Retention
- Entry Storage Systems
- Legacy
- Midrange and Enterprise Storage
- Storage Networking
- HPE Nimble Storage
Discussions
Forums
Discussions
Discussions
Forums
Discussions
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Discussion Boards
Community
Resources
Forums
Blogs
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Receive email notifications
- Printer Friendly Page
- Report Inappropriate Content
HCI optimized for edge, part 6: Cost-effective data security
This technical blog series explains how AI and hyperconverged infrastructure simplify management and control costs at the edge. Part 6 details how HPE SimpliVity protects stored data from both physical and cyber-attacks, including a discussion of the HPE Silicon Root of Trust in the HPE Integrated Lights Out (iLO) chip.

- Part 1: Edge and remote office challenges
- Part 2: Multisite management and orchestration
- Part 3: Cluster resiliency and high availability
- Part 4: Backup and disaster recovery
- Part 5: Space and scalability
Now I want to dive into the subject of data security and explain how it works in an HPE SimpliVity environment.
The ongoing battle against cyberattacks
Security in IT is a constant race without a finish line. As soon as you implement protective measures for your data, someone is trying to find a way to circumvent them. We have seen hackers and malfeasants shift from attacking the environment at the application/OS layer to targeting silicon itself and manipulating firmware to gain entry into platforms post-deployment. One of the most profound attempts was back in 2015 when Apple and Amazon discovered microchips as small as the tip of a sharpened pencil inserted into server platforms they were supplying. Allegedly, these chips were created by a foreign government and added to the servers in the supply chain. Once these systems had been implemented, the chips would essentially make changes to hardware firmware manipulating core operating instructions.
At HPE, our engineering and manufacturing teams create our own firmware and silicon chips, allowing us to forge an immutable bond between the two. The aptly named Silicon Root of Trust is a digital fingerprint of HPE Integrated Lights Out (iLO) firmware burned into the iLO5 chip. The iLO5 chip checks the firmware code to verify the iLO firmware before running it. If a hacker inserts a virus or compromised code that alters the bits and bytes, the Silicon Root of Trust will not run the firmware. Once the iLO5 firmware is verified by the chip, the iLO firmware will go on to verify the UEFI BIOS, System Programmable Logic Device, Innovation Engine, and Server platform services.
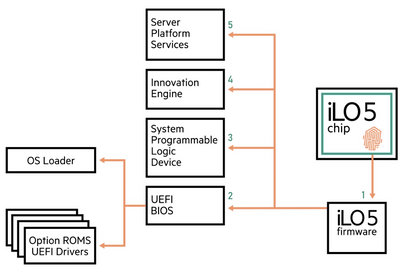
These essential five components are called the Secure Start Base and the server will not start unless all five are verified. If the server is allowed to power on, HPE UEFI secure boot technology verifies the options ROMS and OS loader.
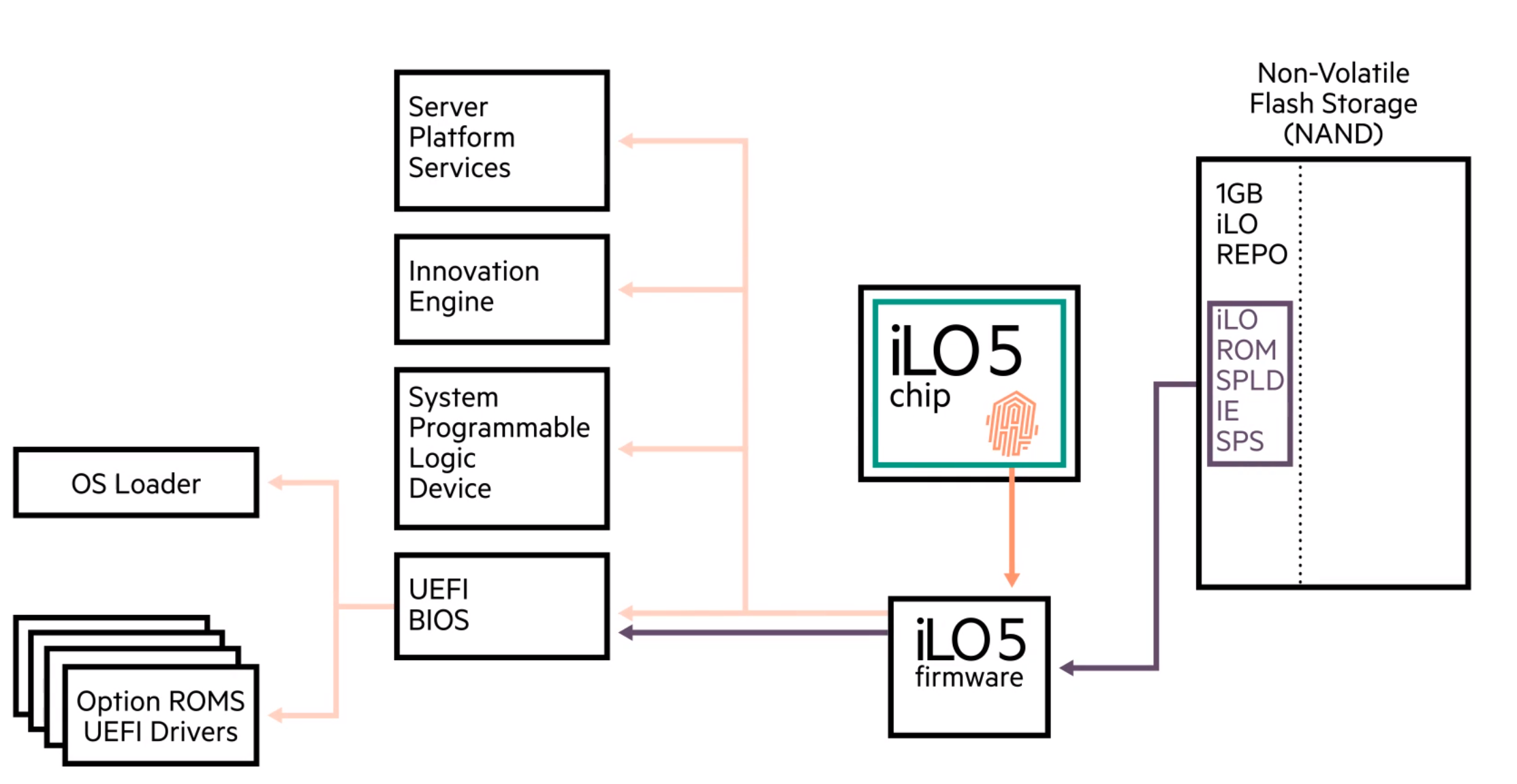
As a fallback measure, factory installed, known good copies of these five essential pieces of firmware are included on the unique non-volatile NAND flash storage. If any of these firmware pieces are not verified in the power-on process, iLO has the ability to securely recover one or all of them from a recovery set before the server is allowed to power on. iLO5 will retrieve a backup copy and verify its integrity before securely reprogramming the component.
This securely trusted change allows HPE chips to monitor these core components protecting infrastructure from lower level attacks and supply chain issues.
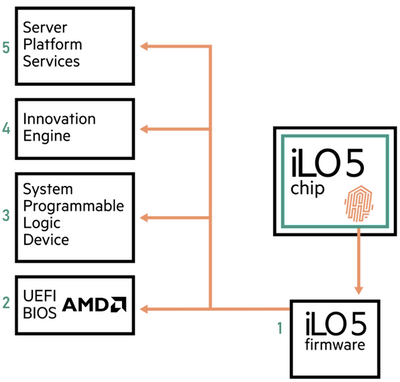
The HPE SimpliVity 325 platform leverages AMD CPUs, tying in the AMD Secure Processor with the Silicon Root of Trust. Embedded in the AMD EPYC system, AMD Secure is a dedicated security processor which manages secure boot, memory encryption and secure virtualization. This process becomes part of the iLO5 Secure Start Base, which means the iLO5 firmware conducts a thorough verification of the AMD Secure Processor and will stop the boot process if any malware is detected. This is done simultaneously while the Silicon Root of Trust verifies the BIOS firmware.
Cost-effectively protecting data from physical attacks
The HPE SimpliVity platform also protects stored data from physical attacks through controller-based data-at-rest encryption (DARE). You can achieve similar protection through relatively expensive self-encrypting drives, encryption performed by operating systems, or features like virtual machine encryption from VMware. These software approaches can be effective, but they add to compute overhead on the system, which costs CPU and memory resources.
DARE is every bit as secure, and it doesn’t consume these additional resources. HPE Smart Array SR Secure Encryption is controller-based DARE for drives connected to HPE Smart Array Controllers. The FIPS 140-2 enterprise class encryption solution complies with regulations for sensitive data, such as HIPAA and Sarbanes-Oxley. When this data protection feature is enabled in HPE SimpliVity nodes, the underlying RAID groups in each node are automatically encrypted. Unlike software solutions, this encryption process is handled by hardware, making it cost-effective and highly performant, and not stealing any resource from the server itself, or from your virtual workloads.
DARE technology requires an encryption key: a random string with the sole purpose of encrypting and decrypting data. This key can be stored locally on the HPE Smart Array controller which requires no management from administrators. Alternatively, keys can be stored remotely on an Enterprise Secure Key Manager (ESKM) which manages all encrypted keys throughout data centers and across remote sites.
Where to go next? Complete solutions from HPE and technology partners
I’ve shared some of the most important features of HPE SimpliVity hyperconverged platform in this blog series to date. It’s only fitting that I wrap up with solutions you can deploy simply. In my final post, I will cover some of the turnkey solutions that HPE offers with our technology partners, to make it super easy for you to migrate your data to this exciting technology for the edge. Stay tuned...
In the meantime, watch this video to learn more about our industry-leading security features: The World’s Most Secure Industry Standard Servers & How HPE Built the Silicon Root of Trust
Get details on HPE iLO server management software here.
Explore the HPE portfolio of AMD EPYC-based solutions here.
Read my entire blog series and learn more about HPE SimpliVity environments.
HCI Optimized for Edge
- Part 1: Edge and remote office challenges
- Part 2: Multisite management and orchestration
- Part 3: Cluster resiliency and high availability
- Part 4: Backup and disaster recovery
- Part 5: Space and scalability
- Part 6: Cost-effective data security
- Part 7: Simple edge configuration

Storage Experts
Hewlett Packard Enterprise
twitter.com/HPE_Storage
linkedin.com/showcase/hpestorage/
hpe.com/simplivity
- Back to Blog
- Newer Article
- Older Article
- haniff on: High-performance, low-latency networks for edge an...
- StorageExperts on: Configure vSphere Metro Storage Cluster with HPE N...
- haniff on: Need for speed and efficiency from high performanc...
- haniff on: Efficient networking for HPE’s Alletra cloud-nativ...
- CalvinZito on: What’s new in HPE SimpliVity 4.1.0
- MichaelMattsson on: HPE CSI Driver for Kubernetes v1.4.0 with expanded...
- StorageExperts on: HPE Nimble Storage dHCI Intelligent 1-Click Update...
- ORielly on: Power Loss at the Edge? Protect Your Data with New...
- viraj h on: HPE Primera Storage celebrates one year!
- Ron Dharma on: Introducing Language Bindings for HPE SimpliVity R...


